Risk assessment




















Academic Publications
Digital traces of offline mobilization
Since 2009, there has been an increase in global protests and related online activity. Yet, it is unclear how and why online activity is related to the mobilization of offline collective action. One proposition is that online polarization (or a relative change in intensity of posting mobilizing content around a salient grievance) can mobilize people offline. The identity-norm nexus and normative alignment models of collective action further argue that to be mobilizing, these posts need to be socially validated. To test these propositions, across two analyses, we used digital traces of online behavior and data science techniques to model people’s online and offline behavior around a mass protest. In Study 1a, we used Twitter behavior posted on the day of the protest by attendees or nonattendees (759 users; 7,592 tweets) to train and test a classifier that predicted, with 80% accuracy, who participated in offline collective action. Attendees used their mobile devices to plan logistics and broadcast their presence at the protest. In Study 1b, using the longitudinal Twitter data and metadata of a subset of users from Study 1a (209 users; 277,556 tweets), we found that participation in the protest was not associated with an individual’s online polarization over the year prior to the protest, but it was positively associated with the validation (“likes”) they received on their relevant posts. These two studies demonstrate that rather than being low cost or trivial, socially validated online interactions about a grievance are actually key to the mobilization and enactment of collective action.
(From the journal abstract)
Smith, L. G. E., Piwek, L., Hinds, J., Brown, O., & Joinson, A. (2023). Digital traces of offline mobilization. Journal of Personality and Social Psychology, 125(3), 496–518. https://doi.org/10.1037/pspa0000338
Cyber-enabled burglary of smart homes
Over the last few years, there has been a steady increase in smart home technology's pervasiveness, to the degree where consumer IoT is part of many homes. As our homes become complex cyber-physical spaces, the risk to our physical security from attacks originating in cyberspace becomes much more significant. Within the literature, there is much discussion about the technical vulnerabilities within the smart home. However, this is often not linked to a rich understanding of how an attacker could exploit them. In this paper, we focus on residential burglary and develop a rich understanding of the process by which residential burglary is committed and the effect of the smart home on this process. By combining two areas of the academic literature, residential burglary and smart-home security, this paper provides an academically grounded discussion that places the nascent vulnerabilities associated with the smart-home into the context of the process by which burglary is committed. The commission of residential burglary is a complex decision-making process, which the public often simplifies into planned or unplanned crimes; this is a dangerous oversimplification. The analysis identifies some increased risk during the target selection stage phase. However, in the short term, residential burglars are unlikely to exploit smart home technology routinely.
Hodges, Duncan. (2021). Cyber-Enabled Burglary of Smart Homes. Computers & Security. 110. 102418
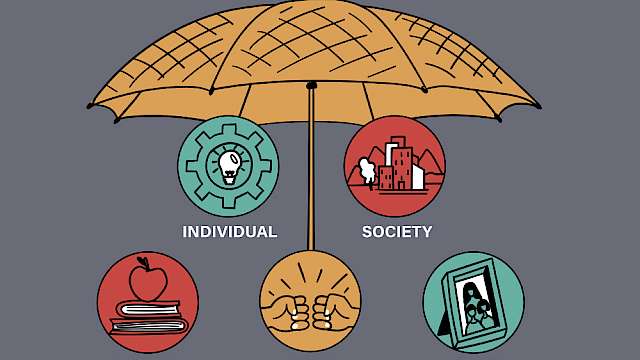
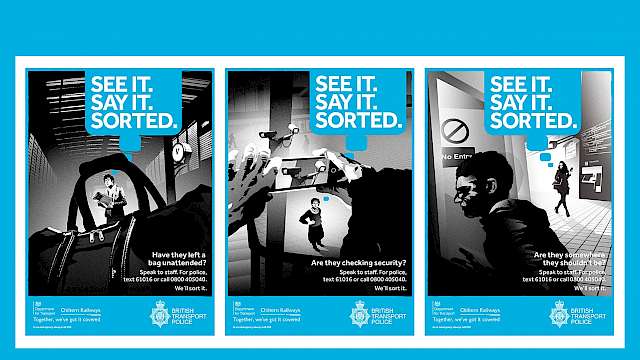
Bystander reporting to prevent violent extremism and targeted violence: learning from practitioners
The willingness of friends or family to share concerns about an ‘intimate’ preparing to perpetrate public, mass violence, such as violent extremism or targeted violence, is considered a possible part of preventative strategies. To understand what is needed to help intimate bystanders share information on potential acts of violent extremism or targeted violence, we conducted 25 semi-structured qualitative interviews with experts in intimate bystander reporting, including law enforcement, social service and mental health providers, faith-based leaders, staff in school threat assessment programs, and community practitioners in California and Illinois. Results showed reporting was impeded by multiple factors, including lack of knowledge about violent extremism and reporting processes, fear of being incorrect, difficulty distinguishing between violent extremism and mental illness, low trust in law enforcement, and lack of standardized reporting processes. Practitioners said reporting could be improved by several interventions, including increasing awareness about reporting processes, improving reporting methods and policies, training community members who can take reports, and increasing trust between community members and law enforcement. Improving bystander reporting for targeted violence and violent extremism in the U.S. requires collaboratively strengthening law enforcement and community capacities based on sound theory, best practices, and monitoring and evaluation.
(From the journal abstract)
David P. Eisenman, Stevan Weine, Nilpa D. Shah, Nicole V. Jones, Chloe Polutnik Smith, Paul Thomas & Michele Grossman (2022): Bystander reporting to prevent violent extremism and targeted violence: learning from practitioners, Behavioral Sciences of Terrorism and Political Aggression, DOI: 10.1080/19434472.2022.2130960
An Evidence Synthesis of Covert Online Strategies Regarding Intimate Partner Violence
This systematic review synthesizes evidence of how people use the internet to deploy covert strategies around escaping from, or perpetrating, intimate partner violence (IPV). Online tools and services can facilitate individuals leaving abusive relationships, yet they can also act as a barrier to departure. They may also enable abusive behaviors. A comprehensive literature search of published and unpublished studies in electronic databases was conducted. Two researchers independently screened abstracts and full texts for study eligibility and evaluated the quality of included studies. The systematic review includes 22 studies (9 qualitative and 11 cross-sectional studies, a randomized control trial [RCT] and a nonrandomized study [NRS]) published between 2004 and 2017. Four covert behaviors linked to covert online strategies around IPV were identified: presence online, granular control, use of digital support tools and services, and stalking and surveillance. The same technology that provides individuals with easy access to information and supportive services related to IPV, such as digital devices, tools, and services, also enables perpetrators to monitor or harass their partners. This review takes a rigorous interdisciplinary approach to synthesizing knowledge on the covert strategies adopted by people in relation to IPV. It has particular relevance to practitioners who support survivors in increasing awareness of the role of digital technologies in IPV, to law enforcement agencies in identifying new forms of evidence of abuse, and in enabling designers of online/social media applications to take the needs and vulnerabilities of IPV survivors into account.
(From the journal abstract)
Grimani, A., Gavine, A., & Moncur, W. (2020b). An Evidence Synthesis of Covert Online Strategies Regarding Intimate Partner Violence. Trauma, Violence, & Abuse, 152483802095798.
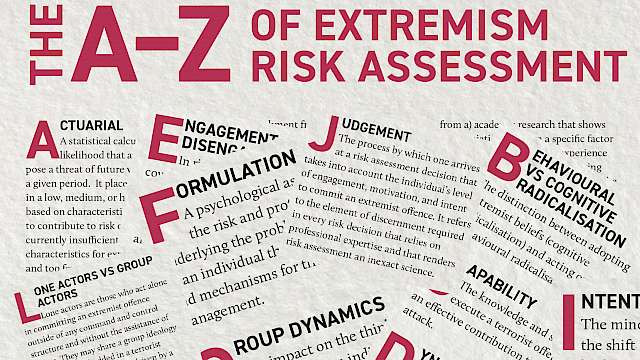
Violent Extremism: A Comparison of Approaches to Assessing and Managing Risk
The task of assessing and managing risk of violence has evolved considerably in the last 25 years, and the field of violent extremism has the potential to stand on the shoulders of the giants of this time. Therefore, the objective of this study was to identify good practice in the risk field and to apply that to the specific area of risk in relation to violent extremism – in order that developments here accord to highest standards of practice achieved so far elsewhere.
Method and Results
We begin by addressing the essential requirement to define the task of assessing and managing the risk of violent extremism – What is its purpose and parameters, who are its practitioners, in what contexts is this activity delivered, and how might any such context both facilitate and hinder the objectives of the task? Next, we map the terrain – What guidance is already available to assist practitioners in their work of understanding and managing the risk of violent extremism, and by what standards may we judge the quality of this and future guidance in the contexts in which is it applied? Finally, we explore options for the development of the field in terms of the empirical basis upon which the risks presented by individuals and the organizations to which they may affiliate are assessed, understood, and managed.
Conclusions
Recommendations are proposed in relation to each of these three areas of concern with a view to supporting the rapid and credible advancement of this growing and vital area of endeavour.
(From the journal abstract)
Caroline Logan and Monica Lloyd. 2019. ‘Violent Extremism: A Comparison of Approaches to Assessing and Managing Risk’. Legal and Criminological Psychology, 24 (1): 141–61. https://doi.org/10.1111/lcrp.12140.
Informal Countermessaging: The Potential and Perils of Informal Online Countermessaging
Online countermessaging—communication that seeks to disrupt the online content disseminated by extremist groups and individuals—is a core component of contemporary counterterrorism strategies. Countermessaging has been heavily criticized, not least on the grounds of effectiveness. Whereas current debates are focused on the role of government and large organizations in developing and disseminating countermessages, this article argues that such approaches overlook the informal production of countermessages. Recognizing the appetite for “natural world” content among those engaged in countermessaging, this article highlights some of the potential benefits of informal approaches to countermessaging. At the same time, the article also acknowledges the risks that may result from closer working between countermessaging organizations and informal actors.
(From the journal abstract)
Benjamin Lee. 2018. ‘Informal Countermessaging: The Potential and Perils of Informal Online Countermessaging’. Studies in Conflict & Terrorism: 1–17. https://doi.org/10.1080/1057610X.2018.1513697.
