Comment

Article
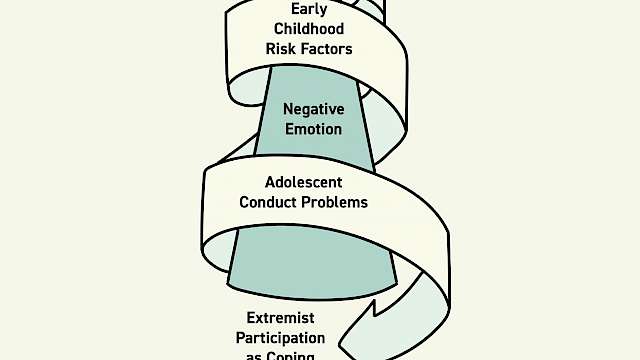
Daniel Koehler
The Radicalisation Pendulum: Introducing a Trauma-Based Model of Violent Extremist Radicalisation
Article
|4 min read
Article
Pete Simi, Steven Windisch
Trauma, Extremism and Criminology
Article
|4 min read

Article
Anna Naterstad Harpviken
Finding the Story: Expanding the Tale
Article
|10 min read

Article
Karen Goodall
Trauma Informed Policing
Article
|4 min read
Article
Vivian Khedari
“I have never hurt anybody”
Article
|7 min read

Article
Ian Barron, Patrick Ashcroft, Gerald Fonville
Police Violence & Child Trauma in the Brazilian Favelas
Article
|4 min read

Article
Lotta Carlsson
Working with victims of torture
Article
|6 min read

Article
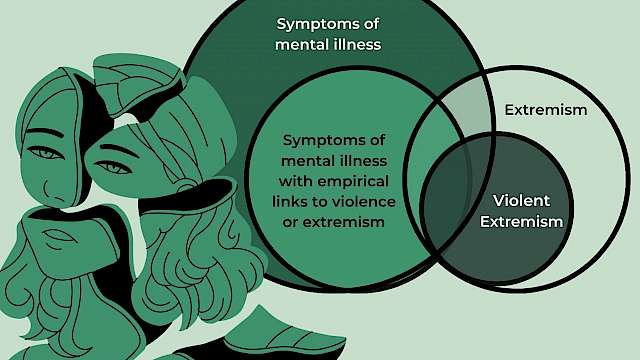
Michael Niconchuk
What to do about mental health in PVE: insights from Central Asia
Article
|7 min read
Article
Olivia Brown
Right-wing extremism online: can we use digital data to measure risk?
Article
|5 min read
Article
Ella Glikson
Emotional over-trust in AI technology
Article
|3 min read

Article
Lina Hillner
Rapport and trust: What’s the difference?
Article
|4 min read

Article
Steven Lockey
Recovering from failure: What can security services do to repair trust?
Article
|4 min read

Article
Rosalind Searle
Trust = confidence + vulnerability The role of the leader
Article
|3 min read

Emma Barrett
The Science of Betrayal: Lessons for security practitioners
10 min read
Article
Paul Taylor
Trusting a Centre model
Article
|2 min read

Article
Stacey Conchie, Paul Taylor
Trust Signals
Article
|4 min read

Article
Andreea-Antonia Raducu
Trust Thy Enemy: Trust and Relationship-Building between Source Handlers and Informants
Article
|4 min read
Article
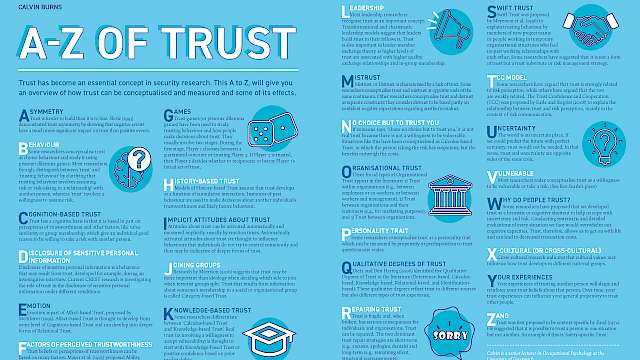
Calvin Burns
A to Z of Trust
Article
|5 min read

Article
Ben Lee
What is Siege Culture?
Article
|3 min read
Article
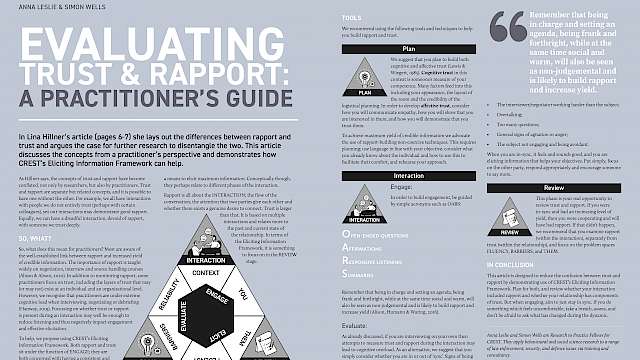
Anna Leslie, Simon Wells
Evaluating Trust & Rapport: A practitioner’s guide
Article
|4 min read

Article
Stacey Conchie
Trust in Security Contexts
Article
|4 min read

Article
David Buil-Gil, Jose Pina-Sánchez, Ian Brunton-Smith, Alexandru Cernat
Bad Data, Worse Predictions
Article
|4 min read

Article
Oli Buckley, Heather Shaw, Leon Reicherts, Richard Philpot, Mark Levine
Technology Lightning Articles
Article
|7 min read

Article
Sophie Nightingale
Identity fraud in the digital age
Article
|4 min read
Article
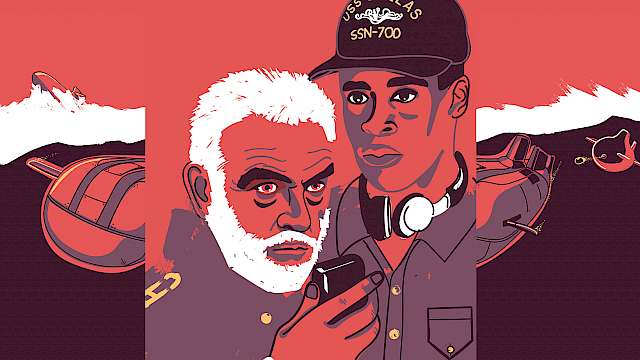
Marion Oswald
‘Give Me a Ping, Vasili. One Ping Only’ Why the Success of Machine Learning Depends on Empowered People
Article
|6 min read
Article
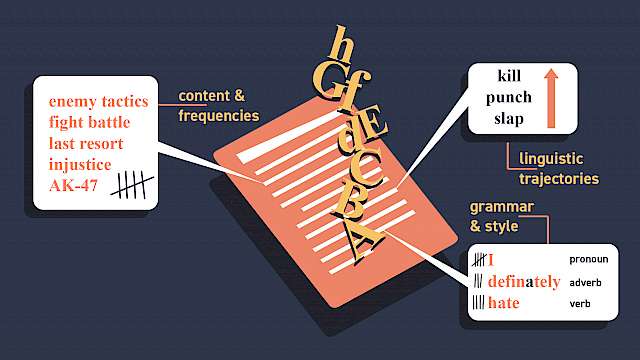
Isabelle van der Vegt, Bennett Kleinberg, Paul Gill
Linguistic Threat Assessment: Challenges and Opportunities
Article
|5 min read
Article
Emma Boakes
Converging security
Article
|4 min read

Article
Erin Grace, Gina Ligon
NCITE: The designated counter terrorism and targeted violence research centre for the US Department of Homeland Security
Article
|3 min read
Article
Zoe Marchment, Paul Gill
Evaluating the Channel Programme’s Vulnerability Assessment Framework
Article
|4 min read
Article
Shanon Shah
How (Not) To Make A Violent Copycat: Lessons From ‘Dark Fandoms’
Article
|4 min read
Article
Chris Baber
Why AI Systems Need to Explain Themselves
Article
|5 min read

Article
Carl Miller
China’s Digital Diplomacy
Article
|10 min read

Article
Mapping a new biometrics landscape
Article
|4 min read

Article
Ben Marshall
Putting the Behaviour into Behavioural Analytics
Article
|4 min read
Article
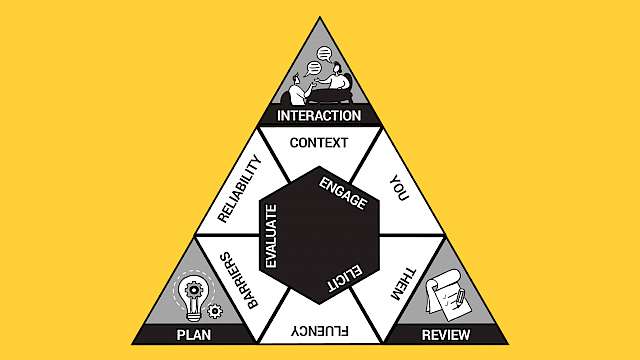
Anna Leslie
The Eliciting Information Framework: A Vehicle For Research Into Practice
Article
|5 min read
Article
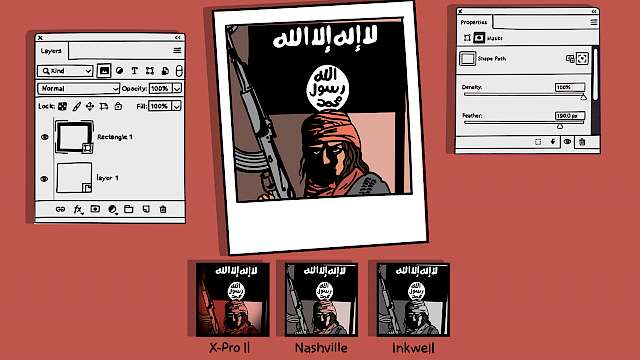
Simon Copeland
Islamic State, Filters, and Photoshop
Article
|4 min read

Article
Andrew Silke, John F. Morrison, Heidi Maiberg, Chloe Slay, Rebecca Stewart
The Phoenix Model: Disengagement And Deradicalisation
Article
|6 min read

Article
Lorraine Bowman Grieve
COVID-19 Conspiracy In Ireland And The Far-Right Nexus
Article
|3 min read

Article
Jason Nurse
Balancing Cybersecurity and Privacy in the Remote Workforce
Article
|4 min read

Article
Laurence Alison, Emily Alison, Sarah Robertson, Michael Humann
The Ground TRUTH After-Action Review Tool
Article
|4 min read
Article
Stephan Lewandowsky, Muhsin Yesilada
The “Infodemic”, Inoculation, And Insurrections
Article
|4 min read

Article
Olivia Brown
Multi-Agency Emergency Response
Article
|4 min read

Article
Jordan Nunan, Ian Stanier
Intelligence gathering during a pandemic
Article
|4 min read

Article
Lorraine Hope, Rachel Zajac, Maryanne Garry
Where was I last Wednesday?
Article
|3 min read
Article
Nathan Smith, Emma Barrett
Lessons From A Rapid Response
Article
|6 min read
Article
Michele Grossman
How Has COVID-19 Changed The Violent Extremist Landscape?
Article
|4 min read

Article
John F. Morrison, Andrew Silke, Heidi Maiberg, Chloe Slay, Rebecca Stewart
The Role Of (Dis)Trust In Disengagement And Deradicalisation
Article
|6 min read

Article
Steven Watson
Risk, benefits, and the affect heuristic in security behaviours
Article
|6 min read
Article
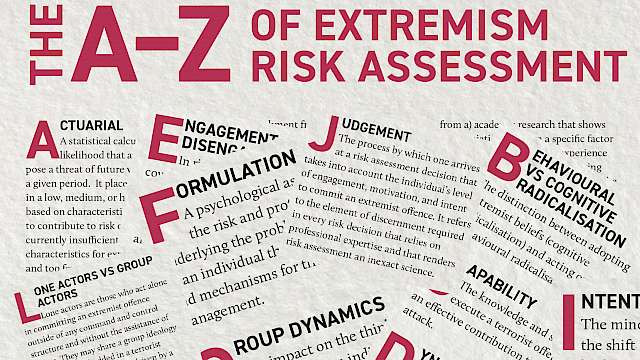
Monica Lloyd
The A–Z Of Extremism Risk Assessment
Article
|5 min read
