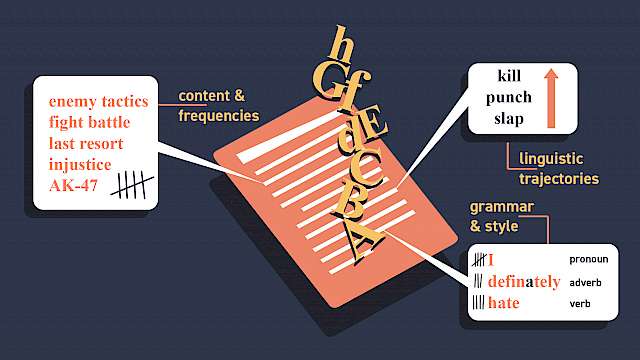
Terrorists from a wide array of ideological influences and organisational structures consider security and risk on a continuous and rational basis.
Of course, the rationality of terrorism has been long observed. Traditionally, authors considered the rational adoption of terrorism as a strategy or a tactic. More recently, and perhaps more interestingly, they have examined the kinds of rational decisions and behaviours that underpin the planning and commissioning of a terrorist attack.
Our research on terrorist planning and decision making in the context of risk led us to analyse over 80 terrorist autobiographies. Here are eight lessons from our study.
1. Terrorist planning
The process of attack planning varies widely. On one end of the spectrum are accounts of attacks being ‘more or less spontaneous’ (Michael Baumann, former left-wing militant) and involving ‘no great pre-planning…done in minutes’ (Gerry Bradley, IRA soldier). On the other end of the spectrum are attack plans being drawn up over six months.
In many cases you could do it all yourself, it will just take a little more time. AND, without taking unacceptable risks. The conclusion is undeniable.
– Anders Breivik on why to forego co-offenders; Breivik, 2011:1461
2. Risk factor
Terrorists conduct cost-benefit analyses. In March 1988, Loyalist Michael Stone single-handedly attacked an Irish Republican funeral in Belfast with grenades and firearms. Stone hoped to ‘take out the Sinn Fein and IRA leadership at the graveside’. Faced with thousands of mourners as well as policing and army units nearby, this was undoubtedly a highly risky attack. ‘Most of the time it was 50:50. I figured would be at least 60:40 against me, but could even be less’ Stone however felt the benefits were too great to pass up. ‘I believed it was worth a risk if it meant the leadership of the Republican movement was wiped out.’
3. Picking a target
Where planning is involved, several targets are often considered. Take, for example, Cathlyn Wilkerson’s account of decision making in the Weathermen. ‘When the proposal was floating about Fort Dix, no one argued against it, but the tension in the air seemed to crystallise into a fine mist…. As yet, however, we knew nothing concrete about the base, or exactly what we were talking about or whether it would be possible. We agreed to investigate other targets as well… One team went to each of the possible sites to do reconnaissance… … The conversation focused on which of the targets we had investigated were feasible. Then we discussed the logistical details required for each action.’
The bank branch was chosen for its lack of adjacent buildings.
– UK left-wing extremist group, Improvised Guerrilla Formation, claims responsibility for an incendiary device attack against a Bristol bank in 2013
4. Internal feelings
Subjective factors play a large role in terrorist cost-benefit analyses. Many accounts of the planning phase note internal feelings of ‘tension’, ‘stress’, ‘frayed nerves’, ‘doubt’, ‘frustration’, ‘paranoia’, ‘fear’, ‘inborn sense of danger’, ‘premonition of disaster’, ‘highly sensitised’, ‘hyper-aware’, ‘anxious’, and ‘scared’. Such feelings were also common during the commission of an attack. Attackers note physiological reactions like ‘handshaking’, ‘heart thumped like a drum’, and an ‘inability to sleep.’
5. Finding the weakest link
Objective security features play a large role in terrorist cost-benefit analyses. For example, Michael Stone’s first assassination target was the Sinn Fein politician Owen Carron. Initially Stone surveilled Carron’s home address: ‘I knew he had two dogs... I knew that all over the house and garden he had the best security and surveillance equipment money could buy. He had cameras and sensors. He even had tin cans tied to a tripwire strung across the field at the back of his house to alert him to the security forces that watched his every move… I ruled out attacking him at his home because he had too much security and I could not get close enough to kill him without being spotted or killed myself. My best option was his constituency advice clinic… was the weakest link in his daily routine.’
6. Nerves and confidence
Terrorists expect security features. They actively search for poor deployment of security. Eric Rudolph’s reconnaissance of the Atlanta Olympics Park noted: ‘Hundreds of security guards and cops patrolled the park. They eyeballed me going through the entrances. But there were no metal detectors, and bags were searched selectively. After sundown, the crowds grew enormous… Security at the park became overwhelmed. They stopped searching bags altogether, and the entrances flew wide open. I knew then that I could smuggle in a bomb.’
7. Perceptions of security
Perceptions of security effectiveness matter more than their simple deployment. For example, this was evident in Gerry Bradley’s account of his PIRA activities. In particular, the use of helicopters in surveillance: ‘The chopper destroyed us. If the chopper was up, you weren’t allowed to move out of a house… Ops were cancelled regularly because of it. They could read the newspaper over your shoulder from the chopper.’
8. Past experience
Perceptions of risk shift with experience. The experience of not being caught for previous crimes leads offenders to downplay the immediate situational risks of their current activity. The same is true for terrorists, as Ann Hansen, a former anarchist noted: ‘A steady diet of small illegal activities had boosted my confidence in our abilities to get away with things. I no longer imagined a cop hiding behind every obstacle and actually found myself feeling quite relaxed out on a mission.’
Copyright Information
As part of CREST’s commitment to open access research, this text is available under a Creative Commons BY-NC-SA 4.0 licence. Please refer to our Copyright page for full details.
IMAGE CREDITS: Copyright ©2024 R. Stevens / CREST (CC BY-SA 4.0)